
Previously, a sophisticated hacking campaign targeting security vulnerabilities in Android, Windows and iOS devices was actually the work of “Western government administrators” who run an “anti-terrorism operation.” A new report By MIT Technology Review.
This campaign in question, that is Gained more and more attention Of the media outlets in the last few weeks, it was the first Written about By Google’s threat research team Project Zero in January. At the time, it was all publicly known No Some went on to a very difficult business: probably an “extremely practical” group employed by “teams of experts” was responsible Target Numerous zero-day vulnerabilities in various leading operating operating systems (there will be a total of 11 later), the researchers wrote.
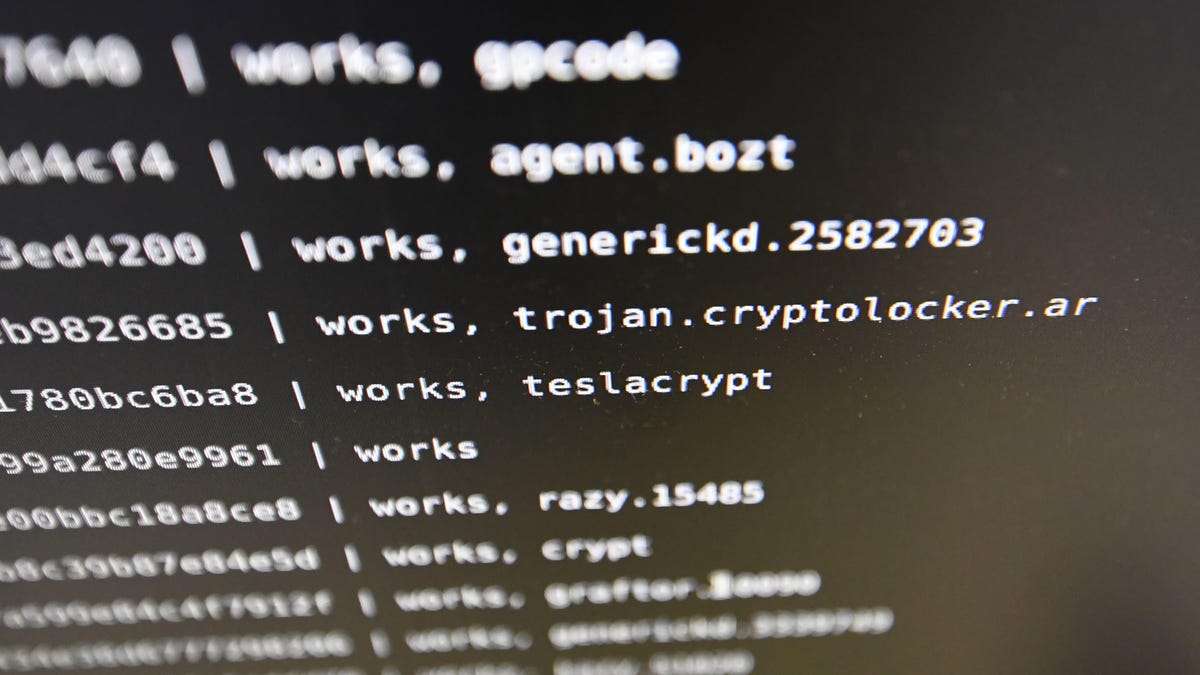
This so-called hacking campaign, which lasted about nine months, is used “Animal watering hole” methodA threatening actor inserts malicious code into a website to effectively “booby trap” it (visitors to that site will later become infected with malware, allowing the hacker to target and increase the compromise of specific targets).
From all this descriptive, the hints naturally pointed to the involvement of some kind of high-level nation-state hackers – though, few would have guessed that the culprits are, in fact, our friends! Still, that case will appear. It is not clear if the government was actually responsible for the attacks, who its targets were, or what the so-called “counter-terrorism” operation was all about. MIT did not disclose how the information came to them.
One thing is for sure: Google’s search and subsequent public disclosure (as well as the company’s decision to address vulnerabilities) have clearly derailed whatever government work is going on. MIT writes Going public, the tech company effectively shut down the “live terrorism” cyber mission, adding that “it is not clear whether Google gave government officials advance notice to stop disclosing these attacks.” This apparently “causes internal divisions on Google and raises questions within the intelligence communities of the United States and its allies.”
G / O media can get commission
Obviously there are too many questions here. First, what was this government doing? What was the threat of “terror” they were investigating? Which website was used to search for so-called terrorists? Given the sensitive political nature of this type of harassment, it is unlikely that we will find any answers to those questions – at least not immediately. But with so little information available, it’s also hard to understand whether Project Zero was justified in getting out of trouble, or what was going on here.
Google obviously knows who the hackers are and MIT Reports Whether the incident should be considered “out of bounds” by the company to make such counter-terrorism operations public, or whether vulnerabilities to “protect users and make the Internet more secure” was a matter of debate in their field. . ”
.